Best way to find and remove mail forwarding rules in Exchange Online
Part of the Microsoft 365 offboarding process involves securing your work environment from data leaks. One such component involves eliminating forwarding messages to external addresses to remove the risk of sharing confidential information. These mail forwarding rules in Exchange Online may have been set by the user or by the previous administration team for legitimate reasons at the time. And it’s important to be aware of all of these as sources of breaches especially when the source can be one or several employees who have left the company.
Often, managing multiple users is problematic because the O365 admin portal is limited by its UI. Admins resort to PowerShell to get it done but don’t always have the skills for elaborate scripting. I’m not a PowerShell power user myself so I usually resort to internet searches to find ready-to-use scripts that can help.
In this article, I’ll describe how to find email forwarding settings in order to turn them off or simply remove them. I’ll demonstrate how to manage them for a single user in the Microsoft 365 portal and some of them can simply be accessed with our third-party tool, sapio365.
Topics:
See how we check for forwarding inbox rules
of deactivated users (at 14:08) in our webinar recording
“Speed up multi-user offboarding in Office 365 with sapio365“
User-defined SMTP email forwarding & mail flow settings
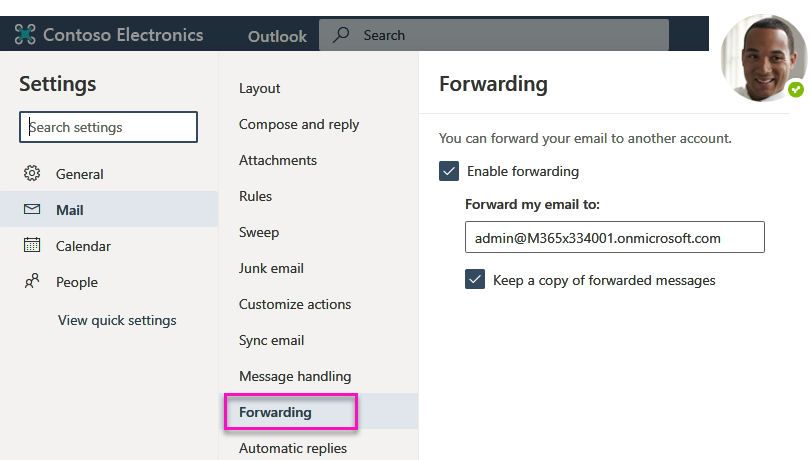
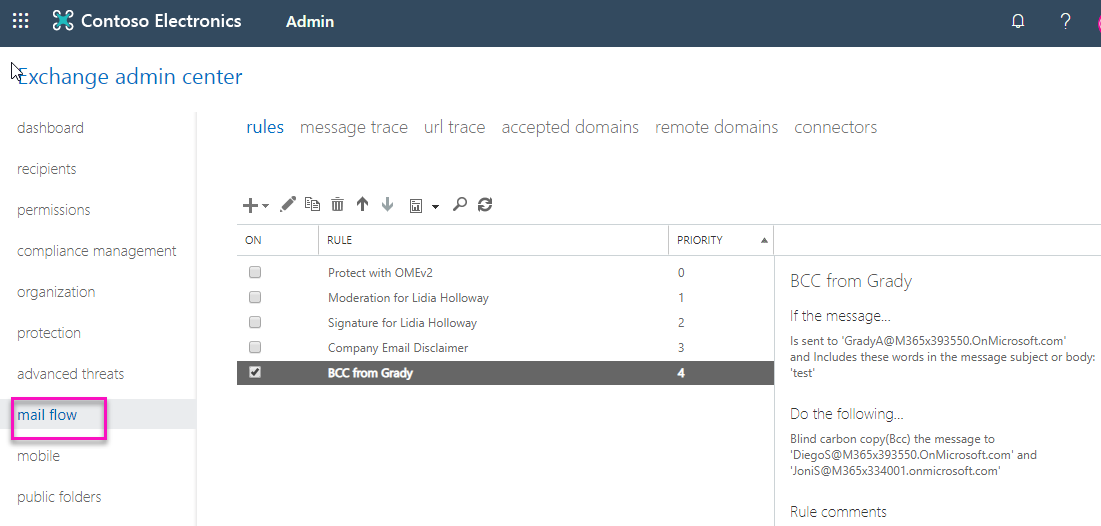
In this scenario, Grady has set up mail forwarding in several ways. One way is via his Outlook settings (see image 1) or SMTP email forwarding. The second way is with inbox rules.
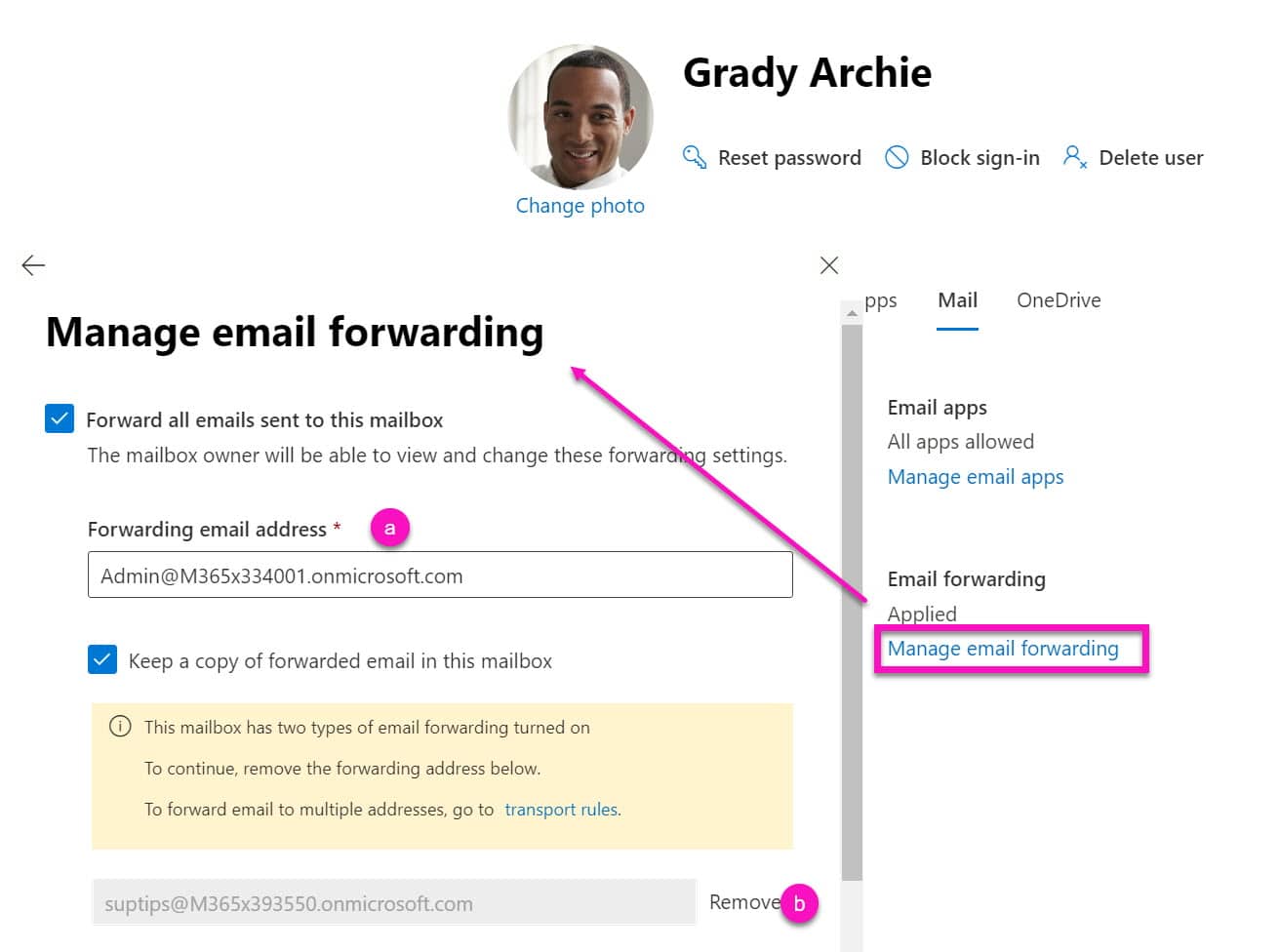
Besides this rule set by the user, previous Exchange admins may have also set forwarding rules on a user’s mailbox in ‘Mail Flow Settings’. Both user-defined SMTP email forwarding (see image 2a) & mail flow settings (see image 2b) can be managed in the admin portal, but only one user at time.
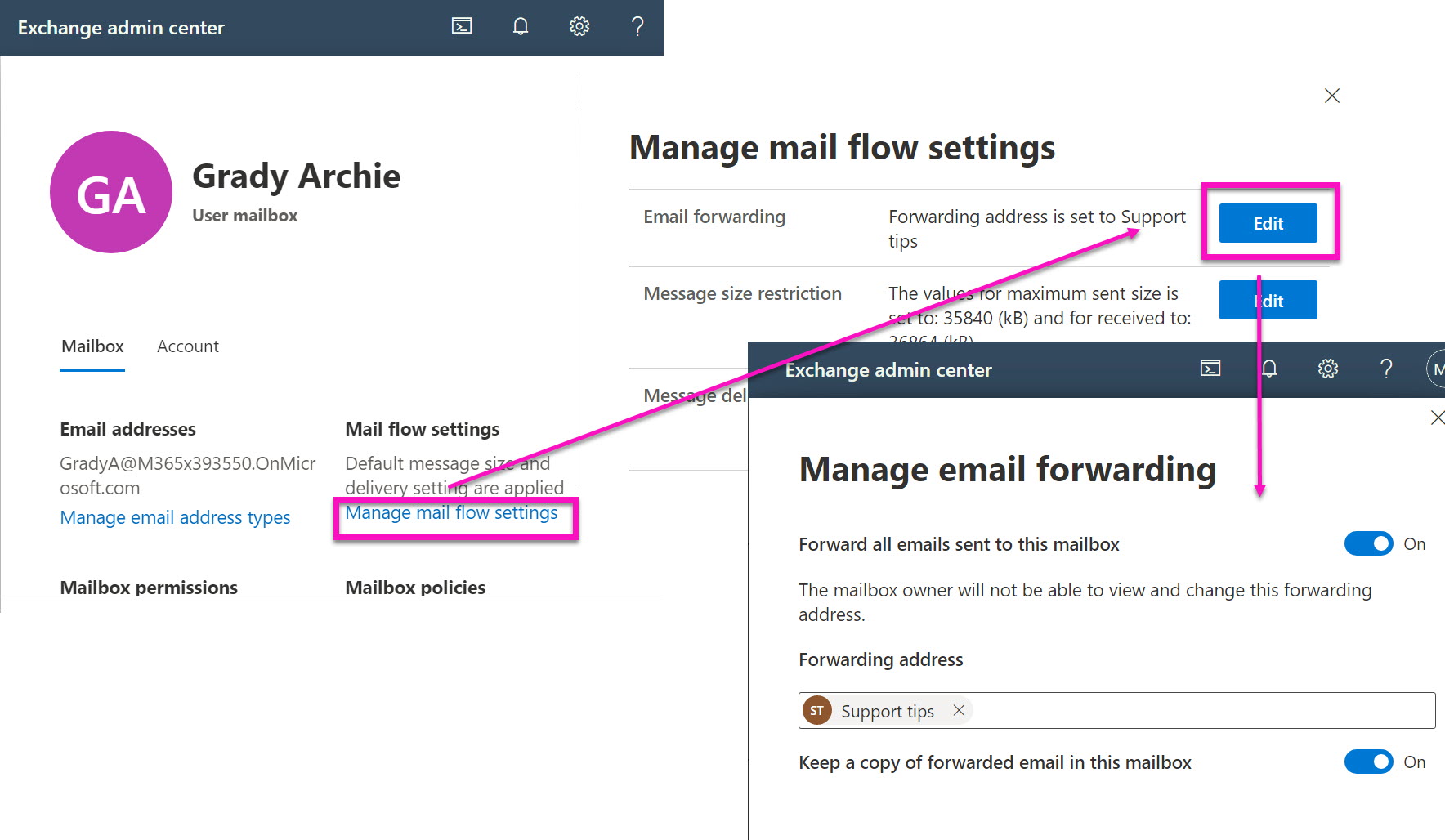
In fact, when this mail flow forwarding rule is set in Exchange Online admin center, the user-defined STMP rule is overridden (see image 3).
sapio365 – a simpler solution
Since it doesn’t make sense to look up this information for each mailbox when offboarding multiple users, admins resort to some commonly used PowerShell scripts that can help.
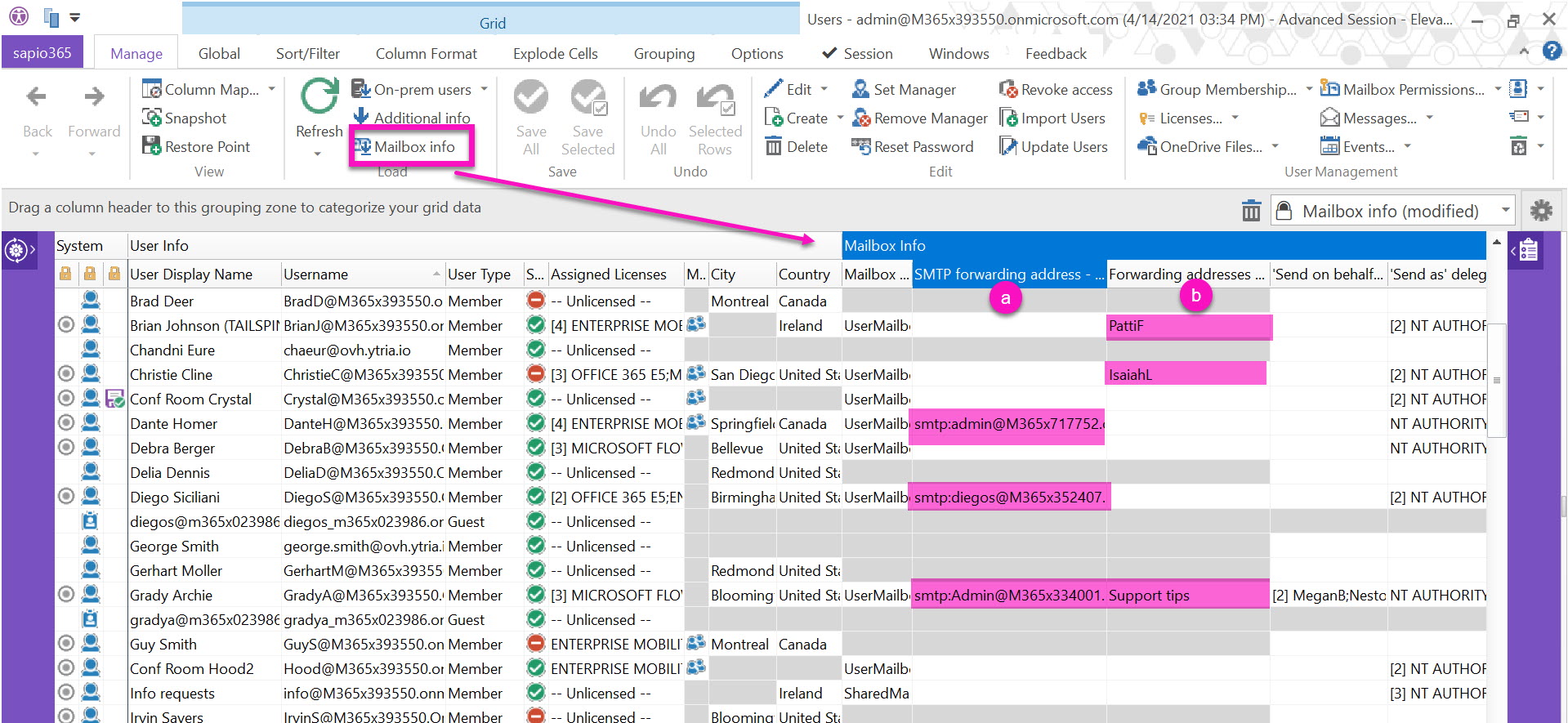
Alternatively, with sapio365 there is no need to code at all—simply choose your users and load their info in 2 clicks!
Briefly, sapio365 is a thick client that installs on your pc and connects you directly to your Office 365 tenant data, so you can see everything in a global view no matter the volume.
You will quickly see and analyze both user-defined SMTP email forwarding (see image 4a) & mail flow settings (see image 4b) for each user. You will also have access to other mailbox settings like ‘Send on behalf of’ and ‘Send as’ delegates.
Large Microsoft 365 communities
Need global views and bulk actions? See how sapio365 helps manage large Microsoft communities.
Interested in articles on Microsoft 365 security?
Find anonymously shared documents and folders and remove permissions
Worried about data leaks? See how sapio365 let’s you can get a handle on what your users are sharing and with whom.
How to clean up teams with guest members
Want to remove guests from some of your Teams? Here’s how you can do it quickly with sapio365.
Who’s signing into office 365 from what location and how often?
Need to identify potential attacks on your user accounts and other unusual sign-in activity? Here a way to do it.
Users’ inbox rules
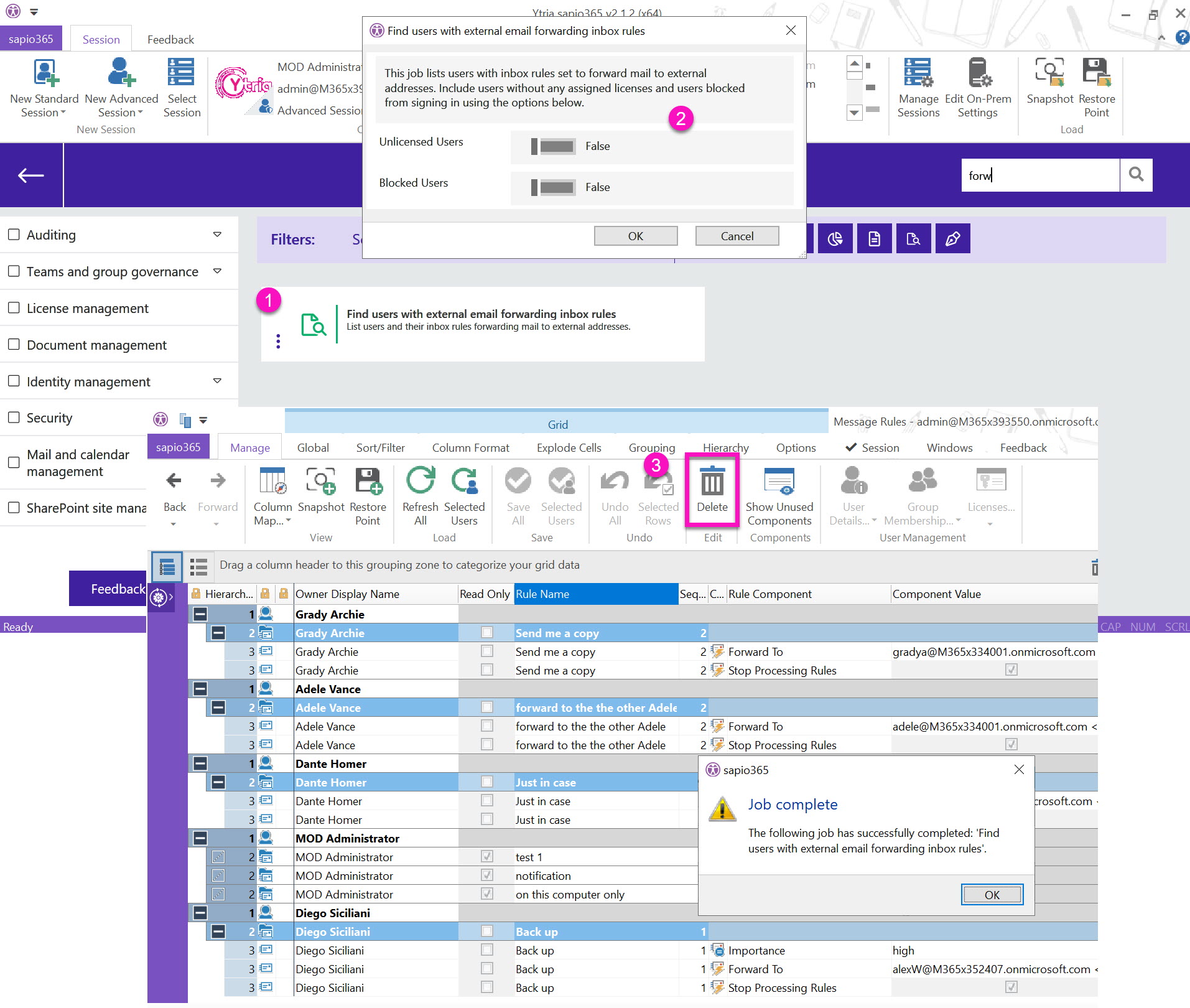
Lastly, let’s look at the most common way users set up mail forwarding rules by navigating to the Rules section of their Outlook settings. Here you can see that Grady has set up two rules, including the “Send me a copy” rule which forwards messages to an external email address (see image 6).
Unfortunately, short of logging in as that user to access his mail rules, I’m not able to see these user-set rules in any of the available admin centers.
The only native solution I found to access them is through PowerShell scripting which becomes a complex task since you’ll need to use a script to get the information to identify forwarding mail rules and another script to remove them. Of course, identifying and removing forwarding inbox rules becomes tedious to do when you’re dealing with several mailboxes, each with its own rules. It even becomes impossible for mailboxes volumes in the thousands because PowerShell requires re-authentication after a certain time.
sapio365 – simpler than PowerShell
sapio365 is an easy and the ONLY alternative to scripting your way to your users’ mail rules.
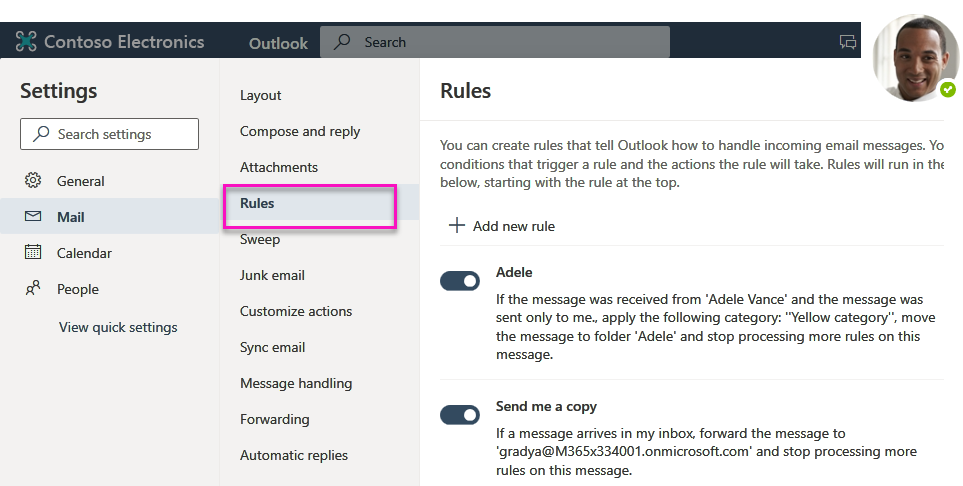
And what’s more, we’ve automated various common admin tasks including an actionable report on externally forwarding inbox rules. It’s as easy as 1,2,3 (see image 7).
- Run the automated job
- Select options
- Delete straight from the report!
In this case, this automatic report used filters to only retain rules that forward emails to external addresses. Each rule is broken down to its components – conditions, actions, exceptions – so that you know exactly what that rule does and if you want to remove it.
The beauty of sapio365 is that it doesn’t require any PowerShell scripting to handle multiple queries and it takes care of the information layout for you. Also, sapio365 may complete high volume tasks in as much time or less than the fanciest PowerShell script but is far more reliable in that it does not time out.
In fact, I can schedule a weekly job in the off-hours. This is to be able to sweep through all the mailboxes looking for rules that forward to external email addresses. When it’s done, I’ll get emailed a report outlining who’s got these inbox forwarding rules set up. Of course like all automated jobs in sapio365, it can be tweaked to actually remove the culprits as it finds them!

Hi Sonia, Can you please help me. My wife has set a few forwarding client based rules on her computer all working off the subject line. Some of her managers emails are received in her Inbox but one particular email is forwarded to a folder. When the email is received, she receives a small grey window on bottom right corner so we know the email has been sent and RECEIVED but does not appear in her Inbox. I can only assume a rule is play and is moving the email. We applied a search to the PST file based on the subject and found the 5 emails with same subject. The email was sent 5 times as we could not find the email.
My question, is it possible to check in reverse, we know we are receiving the email but do not know to which folder it is moved to. The other thing the 2 subject words do not appear in any rule currently set. It appears only one email from manager s moved to a folder but we don’t know why.
If you can please help me it will be much appreciated.
Colin Billau
colin.billau@gmail.com
South Africa
Hi Collin, I can answer you in the context of using sapio365 as I’m not an Exchange Online admin. I suggest that your wife use sapio365 to see her messages because this way you’ll be able to see in which folder they are ultimately in. You don’t need to be an admin to use sapio365, but you do need to be able to consent to external applications (ie. when you create a Standard session, you may not be able to give user consent if the global admin has disabled this in your org.)
So give it a try – download it, install, connect with a Standard session, then go to My Data on the left, and first check the mail rules. You’ll see them broken into components to find any that forwarding action.
Next, load messages. You may want to use date filters to load messages to speed things up, or select all and use subject filter if you know the exact subject line. Check Soft deleted email option (right before the Advanced filters) just in case the rule in play also deletes them.
You’ll see exactly which folders they end up in. Good luck!